WhatsApp Exploit Used to Install Pegasus Spyware
Whatsapp has patched a high-risk vulnerability that allows hackers to remotely install surveillance spyware on mobile devices by simply calling the targeted phone numbers over Whatsapp.
The vulnerability, identified as CVE-2019-3568, can be exploited to install Pegasus Spyware and steal data from targeted mobile devices by placing a WhatsApp call, even when the call is not answered.
According to an advisory published by Facebook, a buffer overflow vulnerability in WhatsApp VOIP stack allows remote attackers to execute arbitrary code on target phones by sending a specially crafted series of SRTCP packets.
Pegasus spyware allows attackers to access an incredible amount of data from victims’ smartphones, including their text messages, emails, WhatsApp messages, contact details, calls record, location, microphone, and camera.
The vulnerability affects all versions of WhatsApp on iOS and Android, except for the latest version, Facebook says: “The issue affects WhatsApp for Android prior to v2.19.134, WhatsApp Business for Android prior to v2.19.44, WhatsApp for iOS prior to v2.19.51, WhatsApp Business for iOS prior to v2.19.51, WhatsApp for Windows Phone prior to v2.18.348, and WhatsApp for Tizen prior to v2.18.15,“.
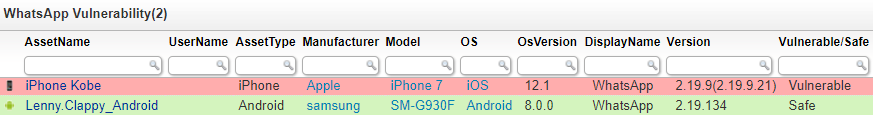
Discover Affected WhatsApp Versions via Intune Scanning
Lansweeper hooks directly into Microsoft Intune’s API to give you immediate visibility into your mobile environment in no time. Regardless of the operating system: both Android, iOS and Windows Phone devices are supported.
Applications installed on the mobile devices are automatically retrieved when you scan your Intune mobile devices. Lansweeper will also retrieve which version of the application is installed, allowing you to report which versions are currently installed on your corporate mobile devices.
If you currently have WhatsApp deployed on your mobile devices, it’s pretty critical that you update them at the earliest opportunity to ensure that you don’t fall prey to this exploit. Our custom color-coded WhatsApp vulnerability report can tell you in no time which devices have a vulnerable WhatsApp version in place and need to be patched.
If you haven’t already, start your free Lansweeper trial and get a report of all affected devices in no time.