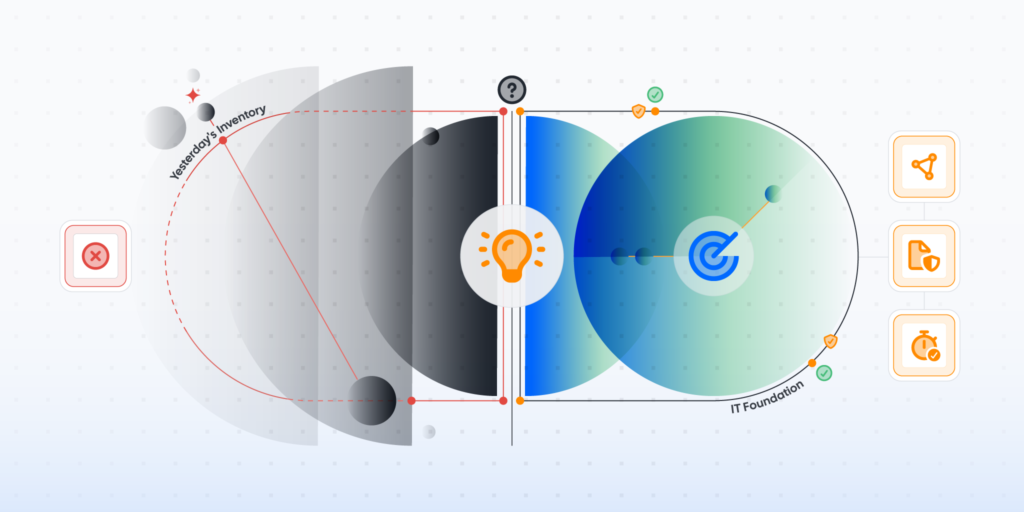
Most organizations don’t have full visibility into their actual digital footprint. In an environment where both IT and security teams are expected to reduce risk and respond faster than ever, that blind spot isn’t just a technical issue, but the reason alignment keeps failing. It’s easy to blame structure, priorities, or even culture. But the real issue is simpler and more fundamental. They don’t see the same environment.
Without a unified asset inventory, IT and security teams operate from different versions of reality. And when the data doesn’t match, neither do the decisions.
Why Can’t IT and Security Align Without a Unified Asset Inventory?
IT and security cannot align without a unified asset inventory because they rely on inconsistent and incomplete data. A single source of truth for asset management ensures both teams work from the same, real-time view of all assets, enabling coordinated action, faster response, and clearer accountability.
In many organizations, IT tracks assets for operational reasons: deployment, maintenance, lifecycle. Security, on the other hand, maps assets to risk: vulnerabilities, exposures, threats.
Both perspectives matter. But when they are built on different datasets, alignment breaks down quickly.
- An endpoint exists in IT’s system but not in security’s
- A cloud instance is flagged as critical by security but unknown to IT
- Ownership of assets is unclear or outdated
The result? Delays, confusion, and gaps that attackers are quick to exploit.
No shared visibility means no shared accountability.
Use Case
One Inventory, Total Control
Automatically build and maintain a single, living inventory of all assets from traditional hardware and installed software, to cloud resources and remote endpoints.
Why IT and Security Still Struggle to Align
The Operational Divide Between IT and Cybersecurity
IT teams are measured on uptime, performance, and service delivery. Their priority is to keep systems running smoothly.
Security teams are measured on risk reduction and incident response. Their focus is to identify and mitigate threats before they escalate.
Different goals lead to different tools, workflows, and reporting structures. Over time, those differences create silos.
Why Collaboration Fails Without Shared Asset Data
Even when teams want to collaborate, they often can’t because their data doesn’t match.
- CMDBs are incomplete or outdated
- Spreadsheets are manually maintained
- Discovery tools operate in isolation
Without reliable asset visibility for cross-team collaboration, every conversation starts with a disagreement: What actually exists in the environment?
That uncertainty slows everything down.
How Siloed Visibility Leads to Finger-Pointing
When an incident happens, gaps in visibility become impossible to ignore.
You’ve heard it before:
- “We didn’t know that asset existed.”
- “That system wasn’t in scope.”
- “We thought the other team owned it.”
These aren’t process failures, they’re visibility failures. And they directly impact response time, risk exposure, and business continuity.
What is a Unified Asset Inventory in 2026?
A unified asset inventory is a continuously updated, centralized record of all assets across IT, cloud, OT, and edge environments, accessible to both IT and security teams in real time. It goes far beyond a static list of devices.
What “Complete Visibility” Actually Includes
Modern environments are dynamic, distributed, and constantly changing. A true inventory must account for:
- Endpoints, servers, and network devices
- Cloud infrastructure and SaaS applications
- IoT and OT assets
- Remote and unmanaged devices
- Rogue or unknown assets
Anything less creates blind spots.
Why Asset Visibility is Foundational to Security and Risk Management
Every security initiative depends on knowing what exists.
You can’t patch a system you don’t know about.
You can’t monitor a device that isn’t tracked.
You can’t secure an environment you can’t fully see.
That’s why asset visibility sits at the core of every major framework and best practice.
It enables:
Without it, everything else is reactive.
What Happens When Asset Visibility is Incomplete?
Modern environments grow fast and often outside of IT’s control. Teams spin up cloud resources. Employees adopt SaaS tools. Devices connect from anywhere.
This creates:
- Shadow IT
- Rogue devices
- Gaps in shadow monitoring
These assets don’t just exist; they operate without oversight.
Hidden Attack Paths and Security Blind Spots
Attackers don’t need sophisticated entry points. They look for what’s overlooked like an unpatched device, an exposed service or a forgotten system. Unknown assets become easy entry points and enable attackers to move laterally across the network once inside. All because something wasn’t visible.
How a Unified Asset Inventory Improves IT-Security Collaboration
Shared Goals Teams Rarely Articulate
Despite their differences, IT and security teams want the same outcomes:
- Reduce risk
- Improve response times
- Maintain operational continuity
A unified asset inventory creates the foundation for those shared goals to become actionable.
From Friction to Alignment with a Single Source of Truth
When both teams rely on the same dataset, everything changes.
- No more duplicate discovery efforts
- No more conflicting asset records
- No more debates about ownership
Instead, teams can focus on what matters: action.
A single source of truth for total asset visibility removes uncertainty and enables faster, more confident decisions.
Measurable Impact
Organizations that unify asset visibility see tangible improvements:
- Faster mean time to respond (MTTR)
- Quicker vulnerability remediation
- Stronger audit readiness
- Reduced operational friction
Alignment stops being aspirational. It becomes operational.
How To Align IT And Cybersecurity Teams Using Asset Intelligence
Alignment doesn’t happen through meetings alone. It requires shared data, integrated workflows, and clear accountability.
Here’s how to get there:
1. Build a single source of truth for asset management
Start by centralizing asset data across all environments (on-prem, cloud, and beyond). This becomes the foundation for both IT operations and security workflows.
2. Automate asset discovery at scale
Point-in-time inventories are outdated the moment they’re created. Continuous, automated discovery ensures new assets are detected as soon as they appear.
3. Integrate asset data into security workflows
Asset data should not live in isolation. It must feed into:
- Vulnerability management
- Patch management
- SIEM and response workflows
This ensures security decisions are based on accurate, real-time information.
4. Define shared KPIs
Alignment requires shared accountability. Examples include:
- Percentage of known vs unknown assets
- Time to detect new assets
- Patch compliance rates
When both teams are measured against the same metrics, collaboration becomes natural.
5. Establish a joint operating rhythm
Regular syncs, shared dashboards, and coordinated planning cycles help maintain alignment over time.
This turns collaboration into a habit, not an exception.
Tools and Best Practices for Unified Asset Inventory
What “Complete” Asset Discovery Really Looks Like
Effective asset discovery combines multiple approaches:
- Agentless scanning for broad visibility
- Agent-based tracking for deeper insights
- Coverage across hybrid and remote environments
No single method is enough on its own.
Why Legacy CMDBs Fall Short
Traditional CMDBs were not built for today’s environments. They rely on:
- Manual updates
- Static records
- Limited integration
The result is predictable: outdated, incomplete data.
Best Practices Checklist
To build and maintain a reliable inventory:
- Use continuous, automated discovery
- Normalize asset data across sources
- Integrate with IT and security tools
- Enable real-time reporting
- Regularly validate asset coverage
Consistency matters more than complexity.
How Lansweeper Enables Unified Asset Visibility
A unified asset inventory isn’t just about seeing assets, it’s about accuracy, scale, and accessibility. Lansweeper provides a continuously updated, centralized view of all IT, cloud, and OT assets, giving both IT and security teams a single source of truth.
With Lansweeper, you can:
- Discover known and unknown assets
- Create a single source of truth for asset management
- Enable cross-team collaboration
- Strengthen security and risk management
Alignment isn’t a people problem; it’s a data problem. When teams share the same visibility, they make faster, smarter decisions, reduce risk, and respond quicker to incidents.
You can’t secure what you can’t see, or align teams that see different realities.
Lansweeper Demo
See Lansweeper in Action
Sit back and dive into the Lansweeper interface & core capabilities to learn how Lansweeper can help your team thrive.
FAQ
-
Why is an IT asset inventory critical to information security operations?
A complete inventory ensures every asset is monitored, maintained, and protected. Without it, vulnerabilities go undetected and risks increase.
-
How does asset visibility reduce cyber risk?
Asset visibility eliminates blind spots, allowing teams to detect vulnerabilities earlier and respond faster to threats.
-
What challenges prevent IT and security teams from aligning?
Siloed tools, inconsistent data, and lack of a single source of truth are the primary barriers to alignment.
-
How can AI improve asset discovery and inventory accuracy?
AI can help identify patterns, detect anomalies, and improve classification—but it depends on accurate asset data to be effective.
-
What are unmanaged assets, and why are they a major security risk in 2026?
Unmanaged assets are devices or systems that are not tracked or monitored by IT teams. They create blind spots that attackers can exploit, making them a major cybersecurity risk.