When Anthropic published its Mythos Preview findings earlier this month, the security community realized immediately that these capabilities represent a seismic shift, forcing an urgent reaction on how to prepare appropriate defenses.
The reaction from the security community is fast and furious: CISOs are reviewing their detection stacks, vendors announce new capabilities and frameworks. The conversation has largely coalesced around a single question: Is your security program ready for the age of AI-accelerated attacks?
It’s a key question to answer, but in our opinion the first question we need to ask ourselves is missing: do we have total coverage and full understanding of what we need to protect?
The Exploit Is the Last Step, Not the First
There’s a seductive logic to framing Mythos readiness as a security detection problem. After all, the threat materializes as an exploit, so the response should be better threat detection, faster response automation and tighter SIEM configuration.
But consider what has to be true for any of that to work.
Before a security tool can detect an anomaly, it needs to know what “normal” looks like for every device, service, and workload in your environment. Before an automated response can contain a compromised asset, that asset has to be known to the system doing the containing. Before a patch can be deployed to close a vulnerability, someone or something has to know where the vulnerable version is running, on which machine, in which network segment, managed by which team.
The entire security response chain is downstream of something that lives in IT operations: a complete, accurate, and current understanding of your technology estate.
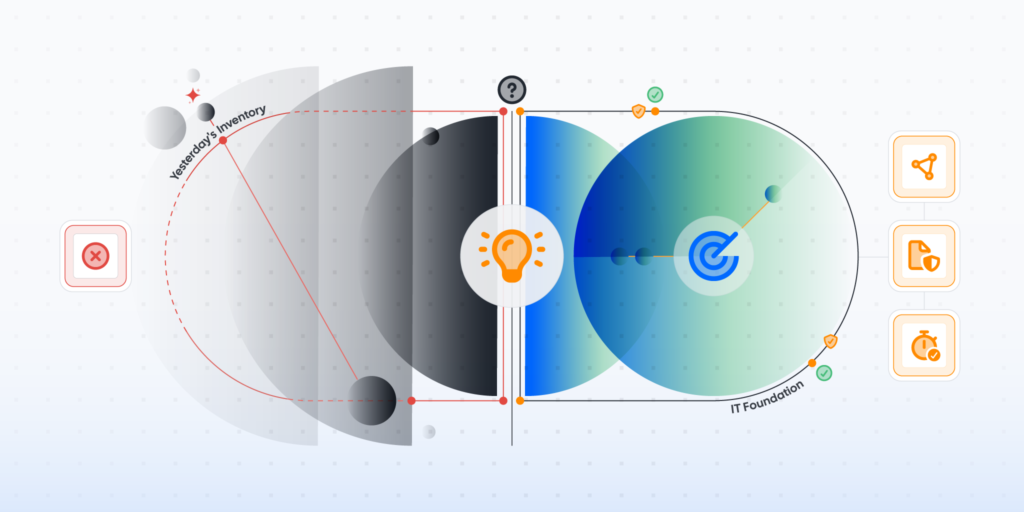
When Exploits Arrive in Hours, Yesterday’s Inventory Is a Liability
For most of the last decade, organizations have operated with a pragmatic tolerance for imperfection in their asset data: CMDBs drift, Discovery scans run weekly, Shadow IT accumulates between audit cycles. IT teams and Security teams maintain separate lists that never quite reconcile. Everyone knows the data isn’t perfect, but the threat environment was slow enough that teams could work around it by manually correlating, investigating, and patching their way through.
The advent of Mythos-like technology presents us with serious questions around the sustainability of this functioning disfunction.
The Three Gaps That Make Organizations Structurally Undefendable
The challenge isn’t just speed. It’s that most technology estates contain three categories of IT knowledge failure that become critical vulnerabilities in an AI-accelerated threat environment.
1. The Completeness Gap
Whether we acknowledge it or not, today’s inventories are still incomplete. There are different teams with different inventories for specific use cases. But where is the single pane of glass across IT, OT, IoT, Cloud? And what about shadow AI tools running on employee machines? Mythos-class threats will not be limited by bad data in your CMDB or blind spots in your inventory.
2. The Consistency Gap
In most organizations, IT and Security operate from different data. IT has its management tooling. Security has its scanner output. The CMDB has something else entirely. When an incident occurs, reconciling these competing pictures takes hours that teams simply will not have. Effective response requires a single authoritative view that both functions share.
3. The Currency Gap
A vulnerability disclosed this morning may be actively exploited by this afternoon. For your response to succeed, your understanding of which systems are affected, which are patched, and which are exposed needs to be measured in minutes. Any organization still operating on weekly discovery cycles is making a potentially very costly bet. The future of security is preemptive but the level of automation this requires simply can’t work without continuously validated data.
These are not security program failures. These are the consequences of IT teams and Security teams operating with different tools and different datasets, with a focus on the actions taken rather than completeness and universality of the estate data.
What “Readiness” Actually Means Now
The conversation Mythos demands is not primarily about better threat detection. It’s about what is needed to close vulnerabilities before the advanced threat capabilities can exploit them.
That means treating asset visibility not as a compliance checkbox or a periodic exercise, but as a continuously maintained operational capability. It means building the data infrastructure that lets automated response systems act with confidence rather than hesitation.
The organizations that will navigate the Mythos era most successfully are not the ones with the most sophisticated detection capabilities but rather the ones where these capabilities are matched with, and enhanced by, total visibility into the technology estate, with context.
Why This Conversation Has a Home in IT
The arguments above reflect what more than a decade of working with IT and Security teams across thousands of organizations has made plainly visible. The gap between what organizations believe they know about their environments and what they can actually confirm has been consistent, persistent, and consequential long before Mythos entered the picture.
Lansweeper has spent twenty years building the infrastructure that closes it. Not because we anticipated AI-accelerated exploitation specifically, but because the underlying problem of incomplete, inconsistent, and stale asset data is not exactly new. We have seen it play out across industries, across geographies, and across every major shift in the threat landscape.
That experience gives us both a perspective and a responsibility. A perspective, because we have observed this problem at a scale and depth that few organizations see from the inside. And a responsibility, because the conversation the industry is now having about AI-accelerated threats requires participants who can speak to the IT foundation, not just the security response layer on top of it.