June 30 marked the start of PrintNightmare, since then a total of 6 separate remote code execution vulnerabilities have been found with the latest being CVE-2021-36958 on August 11.
Back in late June, we created the first blog surrounding PrintNightmare, and ever since then there have been continuous discoveries of more and more flaws in the Microsoft Print Spooler Service which can all lead to possible remote code execution. Due to its popularity, it is not surprising that Ransomware operators have been starting to take advantage of devices that are vulnerable.
PrintNightmare Timeline
If you’ve lost the thread after six Print Spooler vulnerabilities, I don’t blame you. So here is a quick overview of what has happened in the last two months.
- 2021-7-1: CVE-2021-34527 (PrintNightmare)
- 2021-7-8: CVE-2021-1675
- 2021-7-15: CVE-2021-34481
- 2021-8-10: CVE-2021-36936
- 2021-8-10: CVE-2021-36947
- 2021-8-11: CVE-2021-36958
All but the latest vulnerability have been fixed with both out-of-band updates and the regular patch Tuesday updates. If you’d like to check if you’ve got the latest patch Tuesday updates from August installed, you can use our Microsoft August 2021 Patch Tuesday Audit.
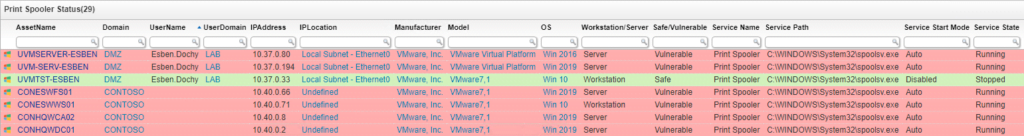
Finding The Print Spooler Service
Since these vulnerabilities keep coming back, you might be interested in checking the status of your Print Spooler services across your IT environment. Luckily we’ve got a report that you can use to get an easy overview of the Print Spooler state and start mode.
How to Disable the Print Spooler Service
Almost all of the Microsoft advisories include instructions on how you can disable the Print Spooler service on your devices, you can do this through Powershell, CMD, GPO, or a combination.
If you have Lansweeper, there is an alternative way using Lansweeper deployment. I have created a simple deployment package that attempts to stop the Print Spooler service and afterward sets the start mode to manual. Combined with a slightly altered version of the report above, you can find all devices that have the Print Spooler service enabled and push the deployment package to them.


