

Uncover hidden vulnerabilities across your network with Lansweeper’s comprehensive asset visibility.

Tailor risk management to your needs with customizable prioritization. Address the most critical threats first for maximum protection.

Streamline risk reduction with seamless integration into your existing tools. Mitigate vulnerabilities swiftly and effectively.
Stay on top of vulnerability resolution and keep your security posture strong with security-focused audit reports.
Despite enormous investments in security, most enterprises still don’t understand the attack surface – which means corporate networks are at risk. Leading security tools focus on threat detection and mitigation, not device discovery and recognition, and must rely on outdated and often inaccurate data. But you can’t protect your assets if you don’t know what you have. Hybrid workspaces, mobile devices, and rapid digitisation have led to nearly uncontrollable IT sprawl.
Complete and up-to-date IT Asset data is a critical starting point for CAASM – first, you need to know what assets you have to protect them. Lansweeper makes it fast and easy to create a comprehensive technology asset inventory with detailed and granular data about all technology assets connected to the network.
Lansweeper’s asset discovery and Credential-free Device Recognition (CDR) automatically detects all network-connected assets – even rogue devices that only briefly touch the network, unmanaged assets, shadow IT, OT, and forgotten, idle devices – creating an always-accurate IT asset inventory.
Lansweeper organizes and contextualizes technology asset data to make it actionable for a variety of use cases. Pre-built and customizable dashboards help you understand patch status, vulnerability exposure, security compliance, software licensing, hardware warranty information and more.
Leverage advanced reporting features to retrieve, analyze and share data as needed, or integrate Lansweeper with Microsoft Power BI to view complete and up-to-date technology asset data alongside other business data for a 360-degree view and improved cyber attack surface visibility.
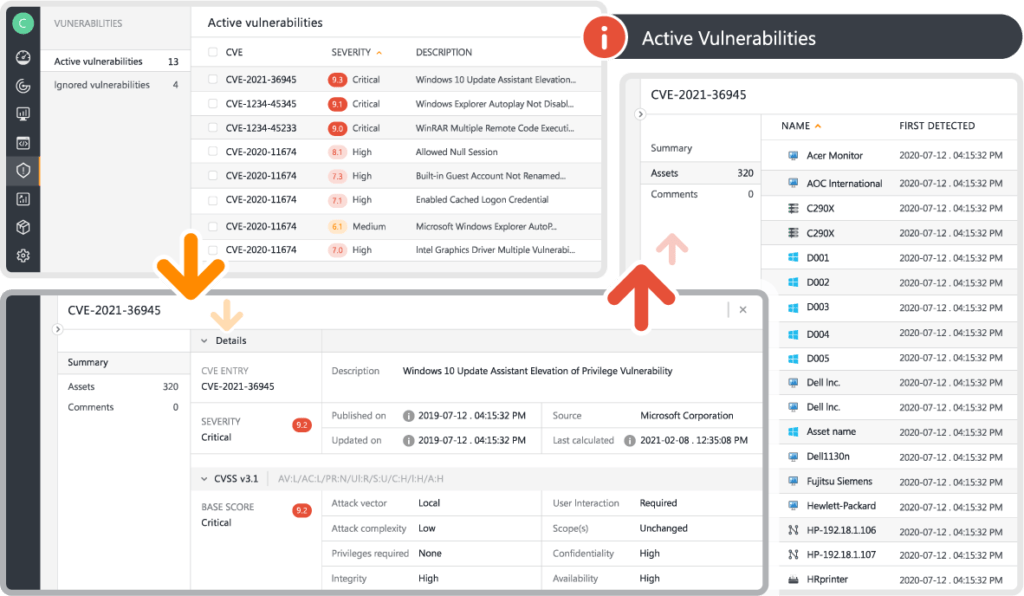
Automated Risk Insights provide a complete list of all known vulnerabilities and customizable risk prioritization, allowing you to tailor your CAASM approach to your organization’s needs.
Pre-made or custom Vulnerability Reports help to locate at-risk devices. Expedite patches and updates, and gain information about the anti-virus status of your Windows machines.
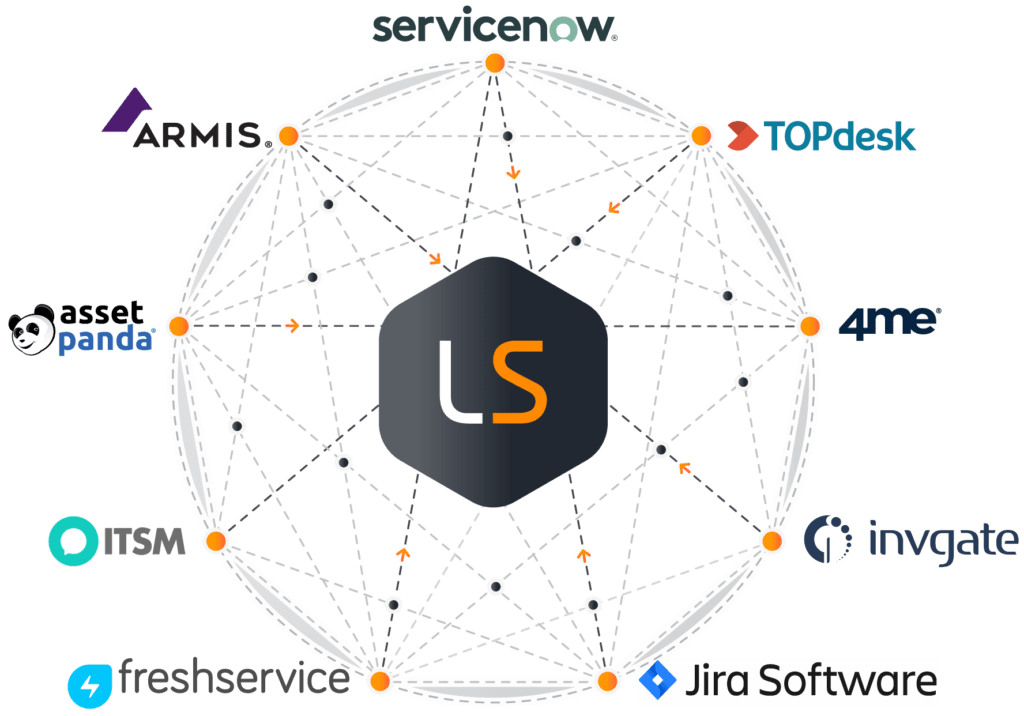
There is no single tool that can do it all, so we focus on what we do best – detecting, and identifying assets on the network. But, we are open and interoperable by design. Through our integrations, Lansweeper seamlessly connects to operational systems across the technology stack, including CMDB, ITSM, SIEM/SOAR tools and others, ensuring they have access to the most up to date IT asset data at all times. Our integrations eliminate data silos and reduce operational overhead by simplifying the process of investigating and remediating security incidents.

Managing complex environments and expanding attack surfaces is critical in an ever-evolving IT landscape. Our Definitive Guide to CAASM dives deep into the essential Cyber Asset Attack Surface Management (CAASM) strategies. Discover how CAASM can revolutionize your approach to cybersecurity, ensuring comprehensive visibility and control over your IT assets.
Explore all our features, free for 14 days.