A study conducted by Trend Micro discovered that 43% of global organizations say the cyber asset attack surface is “spiraling out of control.” Cybercrime has increased by 600% since the onset of the pandemic. By 2025, it will cost companies worldwide about $10.5 trillion every year. The reality is, that if enterprises don’t find a way to properly manage the cyber asset attack surface, disaster is indeed inevitable.
This isn’t news to most organizations and the pressure to find a solution is on. New and innovative solutions in the cybersecurity sector are in high demand. However, before any cybersecurity strategy or solution can be successful, organizations need just one crucial thing: to know what hardware and software assets they need to protect in the first place.
In this blog post, we’ll answer some important questions about cybersecurity in 2024 and beyond, including:
- What is the cyber asset attack surface?
- What is cyber asset attack surface management (CAASM)?
- How does Lansweeper assist with CAASM?
White Paper
Lansweeper for Cyber Asset Attack Surface Management
Gain complete visibility of your technology assets.
What is the Attack Surface – and Why Is It Growing?
The cyber asset attack surface encompasses all points of entry that can serve as attack vectors for unauthorized users to gain access to a system, in order to steal information or launch a cyber attack. Due to rising trends like remote working, digitization, mobility, and cloud computing, the attack surface has expanded exponentially. Organizations are struggling to keep track of the broad mix of physical and virtual assets, operational technology (OT), and Internet of Things (IoT) devices that now comprise the IT estate.
Shadow IT also adds to the problem – the addition of unsanctioned assets consumes up to 40% of IT spending. This means there are many software and hardware assets IT knows nothing about. What’s more, with the majority of organizations offering or planning to offer a hybrid work model, it’s common for employees to sign onto the corporate network using personal, often unprotected devices. As a result, 70% of organizations don’t know what assets they have, which makes them impossible to protect.
What Is CAASM?
CAASM stands for Cyber Asset Attack Surface Management, and it’s just what it sounds like – the process of understanding, protecting, and managing the growing attack surface.
CAASM technology solutions help IT teams detect and identify all software, hardware, and cloud assets connected to the network, as well as vulnerabilities in those assets that could open the door for a cyber attack. CAASM solutions can see which assets have outdated or unpatched software, encryption issues or weak credentials, misconfigurations, or other problems that increase cybersecurity risk. They provide visibility across the entire IT estate, giving IT teams the information they need to manage the attack surface or to act quickly to stop the bleeding should an attack occur.
To work properly, CAASM solutions need access to complete and accurate technology asset data. This data must also be readily accessible so that IT security professionals can isolate assets that pose a threat and take rapid corrective action.
White Paper
Lansweeper for Cyber Asset Attack Surface Management
Gain complete visibility of your technology assets.
How does Lansweeper assist with CAASM?
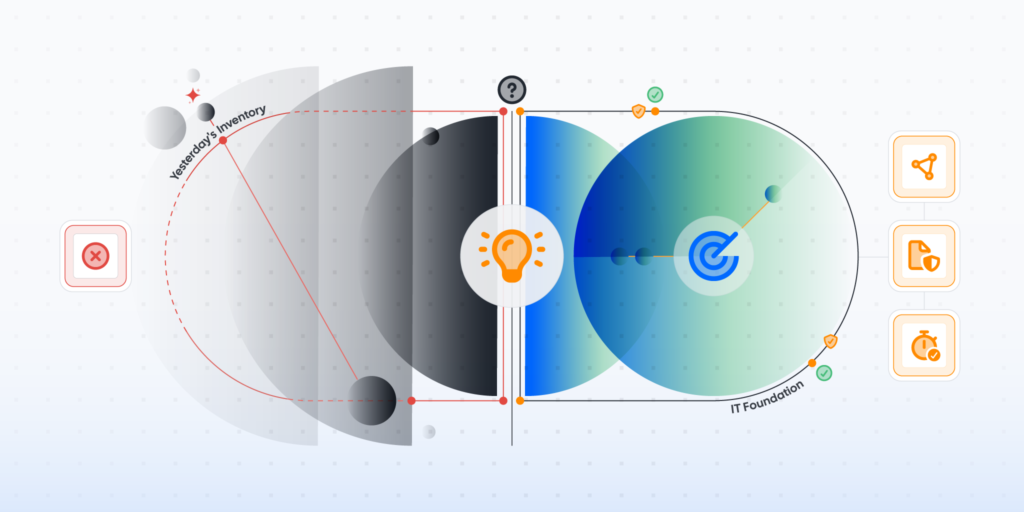
The first step to assessing the attack surface area is knowing what technology assets you have to protect. This makes Lansweeper uniquely positioned to start your CAASM journey, bridging the gap between IT inventory and security.
1. Full Visibility of Your IT Estate
Lansweeper leverages an agentless deep scanning engine and credential-free device recognition (CDR) technology to automatically and continuously discover and recognize all IT assets across your IT infrastructure. Lansweeper sees any asset that so much as touches the network, eliminating shadow IT and rogue devices. and giving you a full comprehensive view of the attack surface.
It creates a comprehensive inventory of your technology assets — servers, laptops, desktops, virtual machines, operating systems, software, OT, and IoT assets — with detailed IT asset data, without the need to install any agent on the devices before you can get started. Because Lansweeper works without agents — and can do an initial scan without the need for credentials — it’s fast and easy to implement.
2. Timely, Accurate Data
Lansweeper extracts data from the “bare metal,” so it’s more accurate and up-to-date. By contrast, most other solutions ingest data from a variety of sources before assembling an inventory, and those sources may be outdated. With highly accurate, reliable, and regularly updated Lansweeper data at your fingertips, you can analyze the attack surface with confidence, pinpoint and eliminate vulnerabilities and security gaps, and strengthen your organization’s security posture.
3. Agent-Based Scanning for Hard-to-Track Assets
With networks becoming increasingly mobile and complicated, certain assets become harder to reach. Think for example of laptops out on the road, devices at remote locations, or machines in protected zones (DMZs). Oftentimes these assets go unmanaged, making them prime targets for security breaches. Lansweeper offers a solution for keeping track of those devices through our installable scanning agent where an agentless approach just can’t reach, offering you the best of both worlds.
4. Asset Data Aggregation
Lansweeper aggregates the technology asset data it gathers from other sources, providing an always-accurate single source of truth to support all business and IT scenarios and enable strategic decision-making. IT security professionals can then leverage this system of record to analyze the attack surface, pinpoint vulnerabilities and security gaps, and strengthen an organization’s security posture to prevent cyber attacks.
5. Better Risk Insights
Lansweeper lets you visualize and analyze data easily, with pre-build or customized dashboards. By leveraging built-in or custom reporting features, you can also share your findings easily. If you integrate Lansweeper with Power BI, you will get a complete 360-degree view of the technology estate.
Lansweeper also gives you a complete overview of all vulnerabilities threatening your assets. The Risk Insights feature draws its information from the VulnCheck, VulDB, CISA, and MS databases for the most up-to-date vulnerability information. You can make your decisions on prioritization based on additional data like the severity, patch availability, and which systems are at risk. Comprehensive network diagrams visualize your IT estate to easily locate compromised devices in your network and see their connections and dependencies.
6. Seamless Integrations
There is no single tool that can do it all, so we focus on what we do best – discovering, detecting, and identifying assets on the network. But, Lansweeper is open and interoperable by design. Through our partnerships, Lansweeper seamlessly connects to a myriad of operational systems across an organization’s technology stack, including CMDB, ITSM, SIEM & SOAR tools, and much more.
You can feed those systems with always accurate and up-to-date IT Asset Data directly, and unlock enriched IT asset data and insights relevant to a broad range of use cases. This eliminates data silos and the operational overhead associated with chasing down information and toggling between tools to investigate and resolve security incidents. An extensive and growing library of APIs enables customers and partners to leverage Lansweeper data to derive their own unique insights.
Minimize the Attack Surface with Lansweeper
IT organizations will continue to grow their technology estate to capitalize on innovation and meet business objectives. That means the attack surface won’t be shrinking any time soon. In fact, Gartner predicts worldwide IT spending will reach $5.26 trillion in 2024, up 7.5% from 2023. Now is the time to put systems and processes in place for CAASM.
Lansweeper provides always up-to-date, trustworthy, IT data from your entire technology estate, faster and more comprehensively than any other solution. A combination of agentless, agent-based, and credential-free discovery guarantees that no asset passes by your network unnoticed. BY aggregating any additional asset data from other sources, Lansweeper becomes your single source of truth for full visibility into your technology estate.
Download our whitepaper, “Lansweeper for Cyber Asset Attack Surface Management (CAASM),” to learn about the features and capabilities of Lansweeper that make it an essential component of your CAASM strategy.
White Paper
Lansweeper for Cyber Asset Attack Surface Management
Gain complete visibility of your technology assets.