Gain complete visibility into your IT environment, prioritize risks effectively, and streamline security workflows — all within an intuitive, cost-effective platform.

Uncover hidden vulnerabilities across your network with Lansweeper’s comprehensive asset visibility.

Tailor risk management to your needs with customizable prioritization. Address the most critical threats first for maximum protection.

Streamline risk reduction with seamless integration into your existing tools. Mitigate vulnerabilities swiftly and effectively.
Stay on top of vulnerability resolution and keep your security posture strong with security-focused audit reports.
Uncover every device with comprehensive Asset Discovery. Lansweeper offers a holistic view of all network assets, including shadow IT and unmanaged devices. This comprehensive visibility ensures no asset goes unnoticed, significantly reducing security vulnerabilities across your organization.
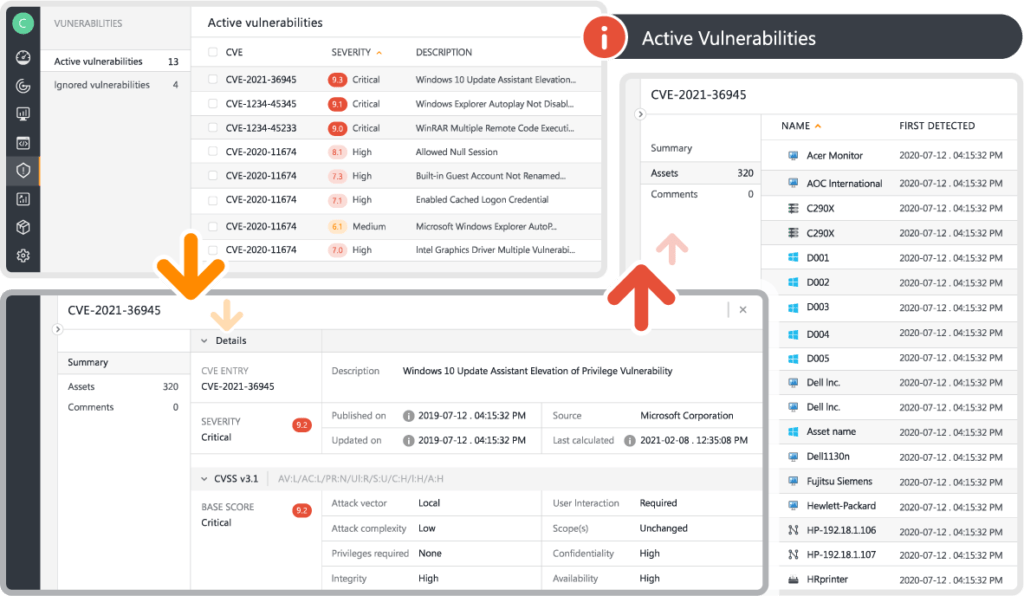
Not all vulnerabilities are created equal. Our platform provides Risk Insights and genuinely customizable risk prioritization, allowing you to tailor your approach to your organization’s needs. This flexibility ensures that the most critical threats are addressed first, optimizing resources and enhancing your security posture.
Integrate effortlessly with various tools and systems, unifying data and streamlining workflows. This seamless orchestration enhances operational efficiency, enabling cohesive and effective security management.
Cybersecurity doesn’t have to be expensive to be effective. Positioned as an affordable alternative to high-cost vulnerability management tools, Lansweeper provides robust cybersecurity measures accessible to businesses of all sizes. This cost-effective approach ensures you can secure your organization without exceeding your budget.
Ensure seamless collaboration between IT and Cybersecurity teams. By providing a unified view of assets, helping to automate processes, and enabling customizable risk prioritization, Lansweeper ensures that your teams can work together seamlessly to protect your organization from evolving threats.
Explore all our features, free for 14 days.