Pro Tips with Esben #39
Passive scanning is one of the newer methods of scanning in Lansweeper. Today we dive deeper into what passive scanning is, can do, and when you should use it.
Passive scanning was the last completely new scanning technology added to Lansweeper. Together with active scanning and agent-based scanning completes the trio of scanning methods. Each of these scanning methods has its own strengths and weaknesses. Today we will take a closer look at what Lansweeper’s implementation of passive scanning means for you, how you can use it, and as always, some reports to go with it.
CDR? Passive Scanning? Device Recognition? Asset Radar?
If you’ve been following Lansweeper for some time, it’s likely you have seen a bunch of terms related to Lansweeper’s implementation of passive scanning. Let’s go over them really quickly so you understand exactly what we mean with each and how they work together.
Passive Scanning
Passive scanning is a method of network analysis that does not require active communication between two systems. From Lansweeper’s perspective, this means that instead of going out and gathering information, we listen and capture whatever information gets presented.
Asset Radar
Asset radar is our implementation of passive scanning. Asset radar can be enabled on any Lansweeper server to passively listen to the network on one or multiple network interface to gather IP addresses, MAC addresses and more. Asset Radar has three modes in can operate in, Disabled, Enabled (logging only) and Enabled (with asset creation).
- Disabled is pretty straight forward, it just turns the feature off all together.
- Enabled (logging only) allows you to use Asset Radar but it creating asset pages for the assets it discovers.
- Enabled (with asset creation) discovers assets and also sends the IP address to Lansweeper’s active scanning to try and do a full deepscan.
Device Recognition
Device recognition is a technology Lansweeper uses to enrich data found in your IT environment. By taking combining specific data points like MAC address, Protocol, and Message Type we generate a unique device fingerprint that gets enriched by our device catalog, a massive data lake with device properties and identifiers.
Credential Free Device Recognition (CDR)
CDR is the combination of asset radar and device recognition to create what we call Credential free Device Recognition. It uses the passive scanning from asset radar to gather data on devices in your network and passes that data on to device recognition which uses the data points to create a device fingerprint which is used to further enrich the data from our device catalog.
Why Use CDR?
Now let’s get to the why. CDR will give you a great view of what has been happening in your network in real-time, it also logs activity for however long you want (depending on what you configure). So it’s ideal to use in wireless networks so you have a log of which devices have connected and if you want to scan them.
Do you want this information without creating more assets? No problem, CDR lets you enabled log-only mode which only logs the devices in your network, and doesn’t pass them on to active scanning to get scanned. This way you still know what has been connecting without any assets being created.
Other use cases like discovering shadow IT, or rogue device detection are also great use cases for CDR. In essence, anything that could benefit from a listening ear on a subnet can utilize CDR.
Managing CDR
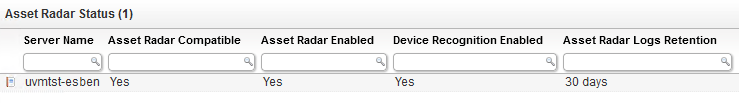
Since CDR is technically limited to the subnet the scanning server it a part of, if you’re planing to roll out CDR to a large part of your organization, you’ll need a number of scanning server to cover all the subnets you want to monitor. As a result, having an overview of the scanning servers and their CDR status might be a great tool to have. Luckily I’ve created an example dashboard (which you can see in the video) with a couple of reports that you can use the maintain a better overview.
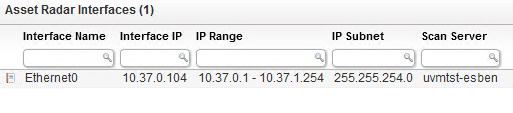
Scanning servers aside, another big component of CDR are the network interfaces used to perform the passive scanning. Similar to the overview for the scanning servers, this will help you see which network interfaces are being used for your passive scanning and the subnets they are active in.
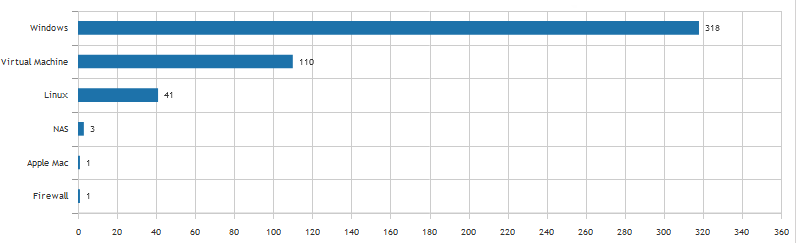
Lastly, regardless of how you use CDR, it might be interesting to have a chart of which asset types have been picked up by CDR. It will let you spot irregularities more quickly.