⚡ TL;DR | Go Straight to the Google Chrome 121 Vulnerability Audit Report
On January 30th, Google released security updates for Chrome 121 for Windows, Linux, and Mac in response to a couple of high-severity vulnerabilities. The issues could lead to arbitrary code execution, which could in turn compromise sensitive data, disrupt services, or cause denial of service. We have added a new report to Lansweeper to help you locate vulnerable Chrome installations.
Chrome 121 Vulnerabilities
The new security update for Chrome 121 includes fixes for 3 high-severity vulnerabilities tracked as CVE-2024-1060, CVE-2024-1059, and CVE-2024-1077. They are all three use after free vulnerabilities in Canvas, WebRTC, and Network respectively. If successfully exploited, they could allow for arbitrary code execution in the context of the logged on user. This could in turn give an attacker access to sensitive data, disrupt services or cause denial of service. You can find more information on Chrome’s release page.
Update Vulnerable Chrome Installations
In order to protect your network and organization against possible attacks, make sure to update all installations of Google Chrome to the latest version (121.0.6167.139 for Mac and Linux or 121.0.6167.139/140 for Windows) as soon as possible.
Google is keeping access to further bug details restricted for now, until a majority of users has had enough time to update their installations first. That way malicious actors won’t be able to leverage the additional information for further attacks.
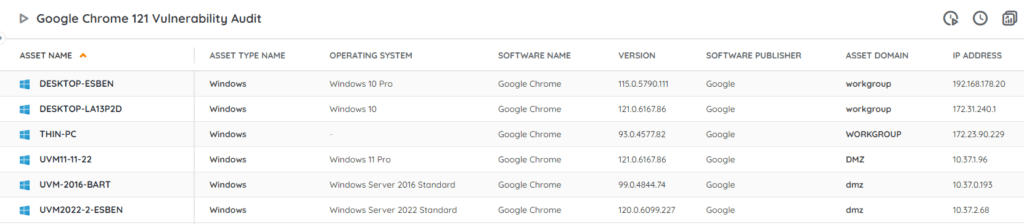
Discover Vulnerable Chrome Installs
Our team has added an updated Chrome 121 audit report to Lansweeper to help you locate any vulnerable installations in your network. This report will give you an actionable list of installations that haven’t been updated to the fixed version yet. You can get the report via the link below.