Endpoint Detection and Response (EDR) is a pivotal aspect of contemporary cybersecurity, particularly in safeguarding endpoints against the growing number of visible and invisible cyber threats. Thanks to its visibility, detection, and response capabilities, cybersecurity experts can rely on EDR to effectively protect their endpoints and mitigate the risk of security breaches in real time.
Even if your organization has unique operational challenges and resource constraints, leveraging an EDR solution can be critical in protecting your IT landscape. While small and medium businesses (SMBs) may not have dedicated threat intelligence teams and fewer resources compared to larger companies, they can turn to cybersecurity solutions and managed security service providers (MSSPs) that offer threat intelligence as part of their services. This allows them to have curated threat intelligence feeds without the need for significant investments.
EDR is integral to a security offense because it provides granular visibility into endpoint activities, enabling your organization to identify and mitigate threats before they escalate swiftly. EDR enhances threat intelligence by leveraging advanced detection techniques, including machine learning, behavioral analysis, and threat intelligence integration. By correlating endpoint data with threat intelligence feeds, EDR solutions can identify patterns and anomalies indicative of malicious activity, bolstering your organization’s ability to pre-empt cyber threats effectively.
What Are Some Examples of Cybersecurity Threats Countered by EDR?
Key components of EDR security include endpoint agents, detection engines, incident response tools, forensic capabilities, and integration with threat intelligence feeds. These components work in tandem to provide comprehensive endpoint protection, enabling your organization to detect, investigate, and remediate security incidents efficiently.
Malware Detection and Removal
EDR solutions are crucial in identifying and eliminating various types of malware, including viruses, worms, Trojans, and ransomware before they can damage endpoints and compromise sensitive data.
Insider Threat Detection
EDR tools are instrumental in detecting suspicious activities initiated by insiders, such as unauthorized access attempts, data exfiltration, and unusual behavior patterns, thereby mitigating the risk of insider threats.
Advanced Persistent Threat (APT) Detection
EDR solutions excel in detecting advanced threats like APTs, which often evade traditional security measures. By monitoring endpoint activities and correlating disparate data points, EDR can uncover stealthy attacks to infiltrate your organization’s network.
Fileless Malware Detection
EDR is adept at identifying fileless malware attacks, where malicious code resides solely in memory. These attacks are more complex to detect with signature-based antivirus solutions. EDR’s behavioral analysis capabilities enable it to detect anomalous activities indicative of fileless attacks.
Zero-Day Threat Detection
EDR solutions are instrumental in detecting and responding to zero-day threats, which exploit previously unknown vulnerabilities. By monitoring endpoint behaviors and analyzing patterns indicative of zero-day attacks, EDR can mitigate the risk of exploitation and data breaches.
Endpoint Visibility and Control
EDR provides organizations with granular visibility into endpoint activities, allowing security teams to monitor user behavior, track software installations, and effectively enforce security policies. This visibility enables proactive threat hunting and rapid incident response.
Incident Response and Forensics
EDR facilitates rapid incident response by providing security teams with real-time alerts, detailed forensic data, and automated response actions. This enables organizations to promptly contain and remediate security incidents, minimizing the impact on business operations.
Compliance and Regulatory Requirements
EDR solutions help you meet compliance and regulatory requirements with comprehensive endpoint security capabilities, including threat detection, incident response, and auditing functionalities. This ensures you comply with industry standards and regulatory mandates governing data protection and cybersecurity.
Choosing the Right EDR Solution
When choosing an EDR solution, it’s essential to consider its capabilities. These include monitoring your systems in real-time, spotting tricky threats before they cause trouble, and automatically dealing with problems when they arise.
It’s also crucial to understand the role of EDR in cybersecurity — it’s like a cornerstone for protecting your computers from sneaky attacks, working alongside traditional antivirus to give you extra layers of defense. So, make sure the EDR you pick adapts to your needs, is easy to set up, and plays well with the other security tools you use.
Is EDR the same as Antivirus?
Endpoint Detection and Response (EDR) and antivirus software serve overlapping yet distinct purposes in cybersecurity:
Antivirus Software
Antivirus software identifies and blocks known malware and malicious files based on signature-based detection methods. It scans files, emails, and other data for known patterns of malicious code and blocks or quarantines them to prevent infection. While antivirus software is effective against known threats, it may struggle to detect and prevent sophisticated, zero-day attacks or advanced persistent threats (APTs).
Endpoint Detection and Response
EDR solutions, on the other hand, provide broader and more advanced capabilities beyond traditional antivirus. They continuously monitor endpoint activities in real-time, collecting and analyzing data on processes, network connections, file activities, and user behaviors.
They use advanced detection techniques such as behavioral analysis, machine learning, and threat intelligence to identify suspicious activities and potential security threats, including known and unknown threats. EDR also offers incident response, threat hunting, and forensic analysis capabilities, allowing security teams to investigate and respond to security incidents effectively.
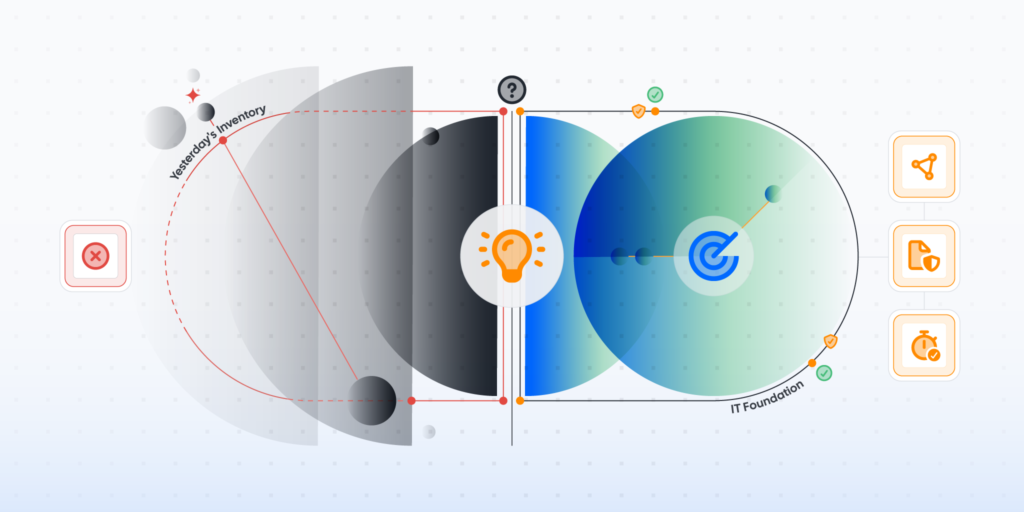
Eliminate EDR Blind Spots with Lansweeper
Unlock comprehensive endpoint security: Discover all connected and unmanaged devices, closing the gaps in your endpoint coverage.
Unlock the full potential of your EDR solution by identifying every device and endpoint that traditional security measures might overlook. Lansweeper offers comprehensive visibility across all network endpoints, ensuring no ‘unmanaged’ gaps in your cybersecurity coverage. Enhance your defenses and experience the benefits firsthand. Don’t miss this chance to fortify your cybersecurity.