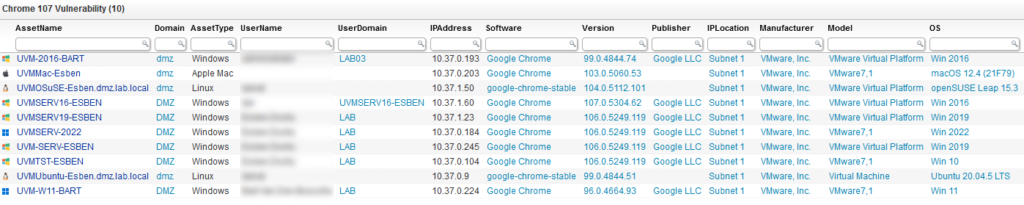
⚡ TL;DR | Go Straight to the Google Chrome Vulnerability Audit Report
Google has released a security update for the desktop version of Google Chrome for Windows, Linux, and Mac in response to a heap buffer overflow vulnerability. According to Google’s own blog, the Chrome vulnerability is already being exploited in the wild. This marks the eighth zero-day vulnerability in Google Chrome exploited in attacks this year. Exploiting this vulnerability could result in crashing of processes, arbitrary code excution, or it could even allow an attacker to bypass security controls, gaining a foothold in the underlying system.
CVE-2022-4135
The vulnerability tracked as CVE-2022-4135 is a Heap buffer overflow in GPU. Google is holding back on releasing any further details for now. They do this to prevent further exploitation of the bug until a majority of users has had a chance to update to the fixed version of Chrome. Heap buffer overflow is a memory vulnerability that can result in data being written to forbidden locations. Attackers can in turn use this to overwrite an application’s memory to manipulate its execution path, leading to unrestricted information access or arbitrary code execution.
Update Vulnerable Google Chrome Installations
In order to protect yourself against the vulnerability mentioned above, Google advises updating all Google Chrome installations to the new fixed version. For Windows that is 107.0.5304.121/.122, for Mac and Linux that is version 107.0.5304.121. You can find more information about the security fix on Google’s release blog.
Discover Vulnerable Chrome Installs
The link below will take you to a special report, created by the Lansweeper team, that will provide you with a list of all computers in your network that don’t have the latest version of Chrome installed yet. This way you can easily locate any installs that are at risk and update them accordingly.