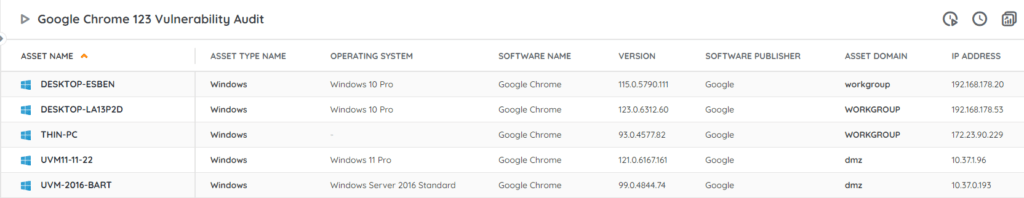
⚡ TL;DR | Go Straight to the Google Chrome 123 Vulnerability Audit Report
On March 26th, Google released security updates for Chrome 123 for Windows, Linux, and Mac in response to 7 vulnerabilities some of which are critical or high severity. When successfully exploited the issues can lead to remote code execution, which could in turn compromise sensitive data and disrupt services. We have added a new report to Lansweeper to help you locate vulnerable Chrome installations.
Google Chrome 123 Vulnerabilities
In total, this security update addresses 7 vulnerabilities in Chrome. 2 of these vulnerabilities were successfully exploited at the Pwn2Own Vancouver 2024 hacking competition.
- CVE-2024-2886 is a high-severity use after free weakness in WebCodecs that allows attackers to perform arbitrary reads/writes via crafted HTML pages.
- CVE-2024-2887 is a high-severity type confusion weakness in WebAssembly that was used in a double-tap remote code execution exploit using a crafted HTML page and targeting both Chrome and Edge.
You can find more information about these and other vulnerabilities on Chrome’s release page.
Update Vulnerable Chrome Installations
The Zero Day Initiative gives publishers 90 days to patch their security flaws demoed at Pwn2Own before they publicly disclose the bug details. Google only took 5 days to release their security update. Still, it is advisable to update your Chrome installations to the fixed version (123.0.6312.86/.87 for Windows and Mac and 123.0.6312.86 for Linux) as soon as possible to protect your network against possible attacks.
As always, Google is holding off on releasing further bug details until a majority of users has had a chance to update their installations. That way malicious actors won’t be able to leverage the additional information for further attacks.
Remember to Update Microsoft Edge
Since Microsoft Edge is also a Chromium-based browser, we can expect an Edge security update soon to respond to the same vulnerabilities. You can always check what version your instances of Edge are on using our Edge Version Audit Report. This report will give you an overview of all instances of Microsoft Edge in your environment along with their version number.
Discover Vulnerable Chrome Installs
We have added an updated audit report to your Lansweeper installations to help you locate any vulnerable instances of Google Chrome in your network. This report will give you an actionable list of installations that haven’t been updated to the fixed version yet. You can get the report via the link below.