Vulnerability management is a critical component of cybersecurity that focuses on identifying, assessing, prioritizing and mitigating vulnerabilities in an organization’s systems, networks and applications. It plays a crucial role in maintaining the overall security posture of an organization and protecting its valuable assets from potential threats.
Vulnerability management is important for a number of reasons, including risk reduction, compliance, asset protection, patch management and business continuity. Setting service-level agreements (SLAs) for vulnerability management helps teams take a proactive approach to securing the IT estate and is vital for maintaining a strong security posture.
Lansweeper assists with vulnerability management by providing comprehensive IT asset management and network inventory capabilities. It leverages deep scanning to scan your network and discover all devices, including servers, workstations, network devices, OT, IoT and virtual assets. Lansweeper also conducts vulnerability scans, checks software versions and missing patches, and identifies known vulnerabilities. By integrating with patch management and other security tools, such as SIEM solutions and ticketing systems, Lansweeper enables organizations to effectively identify, prioritize and remediate vulnerabilities, enhancing their overall security posture.
Let’s dive a bit deeper into the importance of setting up a vulnerability management SLA, and how Lansweeper makes the process easier.
What Is a Service Level Agreement?
An SLA is a formal agreement or contract between a service provider and a customer that outlines the level of service the provider is expected to deliver. SLAs define the specific services, performance metrics and responsibilities to which both parties must agree.
The purpose of an SLA is to establish clear expectations and accountability between the service provider and the customer. It ensures that both parties have a common understanding of the services to be provided, the quality standards to be met, and the remedies or consequences if those standards are not achieved.
How are SLAs used in vulnerability management?
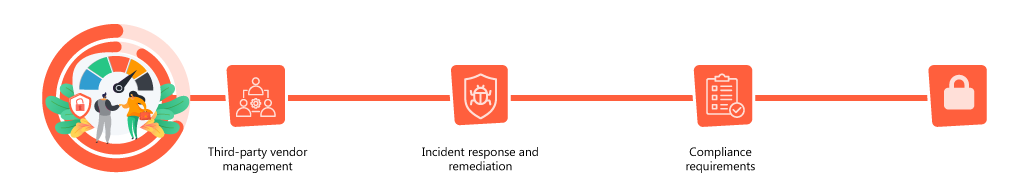
SLAs provide a framework for setting expectations, establishing accountability,and ensuring that the necessary measures are in place to effectively manage vulnerabilities within an organization or in partnership with external service providers. Here are a few ways SLAs can relate to vulnerability management:
- Third-party vendor management: Organizations often rely on third-party vendors for various services, including vulnerability assessments, penetration testing, or managed security services. When engaging with these vendors, organizations can establish SLAs that define the expected level of service and performance in terms of vulnerability identification, reporting and remediation. SLAs can specify the frequency of vulnerability scans, the timeframe for patching critical vulnerabilities, and the quality of deliverables.
- Incident response and remediation: In cases where organizations have internal teams responsible for vulnerability management, SLAs can establish the timeframes within which vulnerabilities should be addressed based on their severity or criticality. This ensures a timely response to vulnerabilities and helps prioritize remediation efforts.
- Compliance requirements: SLAs may include specific requirements related to vulnerability management and security practices, which can involve maintaining a vulnerability management SLA and adhering to industry best practices for vulnerability scanning and patch management. An SLA serves as a mechanism to enforce compliance with these requirements.
Benefits of setting SLAs for vulnerability management
SLAs for vulnerability management provide several benefits. They help organizations set clear guidelines and expectations regarding the vulnerability management process. By defining specific service level agreement metrics, timeframes, and responsibilities, SLAs ensure that all parties involved have a common understanding of what needs to be accomplished. This helps to improve collaboration between teams, reducing the chance of misunderstandings and getting everyone on the same page.
SLAs establish accountability by clearly defining the roles and responsibilities, and setting measurable targets and key performance indicators to allow for objective performance assessments. This promotes a sense of responsibility and encourages timely and effective vulnerability management practices.
SLAs help teams prioritize their work to ensure that the biggest threats are addressed quickly, by specifying response dimes and remediation deadlines. This also helps teams allocate resources effectively.
Key factors in setting SLA for vulnerability management
When creating a service level agreement definition for vulnerability management, there are several key factors to consider that help to ensure the SLA is comprehensive, realistic and aligned with the organization’s goals and requirements. First, be sure to establish a clear framework for assessing and prioritizing vulnerabilities based on their severity and potential impact on the organization.
Once you’ve determined the order of priority, define the expected response time for acknowledging and addressing vulnerabilities once they are identified, including reporting, assessments, and initiating the remediation process. Complete this exercise for each type of vulnerability.
Next, outline escalation procedures for exceptional situations in which vulnerabilities are not being addressed within the agreed-upon timeframes. You should also determine the frequency and format of vulnerability management reporting for stakeholders. Reports should include information on vulnerability scans, identified vulnerabilities, remediation progress and overall vulnerability management performance.
Best practices for SLA management
- Regularly reviewing and updating SLAs
- Establishing clear communication channels
- Providing training and support to teams
Setting up SLAs for vulnerability management is a critical activity and should not be taken lightly! Here are some key best practices:
Maintaining a Service Level Agreement (SLA) for vulnerability management involves ongoing management and monitoring to ensure that the agreed-upon service levels are consistently met. Here are some best practices for maintaining an SLA for vulnerability management:
- Monitor performance: Continuously monitor the performance of vulnerability management activities to ensure they align with the SLA. Monitor key service level agreement metrics such as vulnerability scan frequency, patch deployment timelines, vulnerability resolution timeframes, and overall vulnerability detection and remediation rates. Use automated tools and reports to track and measure performance against SLA targets.
- Set up real-time alerting: Set up alerts for critical vulnerabilities, missed patching deadlines or any other SLA-related issues, so you can take immediate action to address any emerging vulnerabilities or service level gaps.
- Communicate! Maintain open and transparent communication with stakeholders regarding SLA performance and any relevant changes. Provide regular updates on vulnerability management remediation activities, including progress, achievements and challenges, and establish clear channels for stakeholders to provide feedback or raise concerns related to the SLA and actively address their inquiries or suggestions.
- Document everything: Maintain comprehensive documentation and records of SLA vulnerability management activities, including vulnerability scans, patching logs, incident reports and remediation actions. These records serve as evidence of compliance with the SLA and can also support audits or regulatory requirements.
- SLA Review and Renewal: Finally, be sure to establish a process for reviewing and evaluating the SLA periodically, to allow for adjustments or updates based on changing security requirements, emerging threats or organizational changes. Regular review ensures that the SLA remains relevant and effective in supporting the organization’s vulnerability management efforts.
The benefits of using Lansweeper for vulnerability management
Using Lansweeper for vulnerability management provides several key advantages. Lansweeper scans and inventories all devices connected to your network and provides a comprehensive IT asset inventory, which creates a solid foundation for SLA vulnerability management. The platform includes built-in vulnerability scanning capabilities that leverage various databases and security feeds to scan devices and identify known vulnerabilities. You can create specific SLAs for specific ticket types, priorities, sources or users, and leverage built-in or custom filters, reports or widgets to find tickets where SLAs are not respected. Through automation, you’ll save time and effort while implementing regular and consistent vulnerability assessments across the network.
Lansweeper integrates with popular patch management systems, enabling you to automate patch deployment and track patch compliance. It identifies missing patches and outdated software versions, helping you prioritize and streamline the patching process, and ensure that critical security patches are applied promptly, reducing the risk of exploitation.
Lansweeper tracks and manages vulnerabilities associated with each asset in its inventory, and provides a centralized repository where you can view vulnerability details, associated severity levels, and recommendations for remediation. This allows you to prioritize and manage vulnerabilities based on their criticality and impact on your environment. In addition, Lansweeper offers extensive reporting capabilities for vulnerability management, including pre-built vulnerability reports and the ability to customize reports to meet your needs.
Learn more about Lansweeper for Vulnerability Management. New to Lansweeper? Try it for free!