
Just a short time after the previous Dell SupportAssist vulnerability (CVE-2019-3719), a new critical vulnerability has been disclosed (CVE-2019-12280) which opens systems with an unpatched version to DLL hijacking attacks. With the custom color-coded audit below, you can quickly audit your companies IT network and discover any vulnerable computers.
The official Dell security advisory (DSA-2019-084), mentions Peleg Hadar, an Israeli security researcher, as the person who brought the vulnerability to their attention and details that both their SupportAssist for business PCs and SupportAssist for home PCs are affected.
Dell SupportAssist, formerly known as Dell System Detect, checks the health of your computer system’s hardware and software. The software has been designed to interact with the Dell Support website and automatically detect the Service Tag or Express Service Code of your Dell products. The new vulnerability CVE-2019-12280, lies in the proactive monitoring component created by PC Doctor. This component has a fault in the dynamic link library (DLL) which allows attackers to load an unsigned DLL into the service.
Since Dell SupportAssist comes pre-installed on most Dell computers, it is critical that you check whether your Dell machines have a patched version. For SupportAssist for home PCs this is version 3.2.2. For SupportAssist for business PCs this is version 2.0.1.
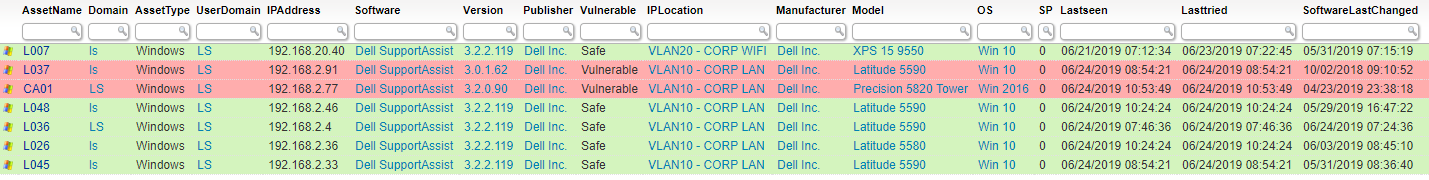
Get A Report of Vulnerable SupportAssist Installations
Similar to the previous SupportAssist vulnerability we covered. If you currently have Dell SupportAssist deployed in your environment, it is critical that you check whether the installations have been updated or not. Our custom color-coded vulnerability audit you can tell you in no time which devices have a vulnerable Dell SupportAssist version in place and need to be patched.
If you haven’t already, start your free Lansweeper trial and get a list of all vulnerable Dell SupportAssist versions in no time.


