
NVIDIA issued a security bulletin and update to fix three high and medium severity security issues in the NVIDIA GPU Display Driver that could lead to code execution, denial of service, escalation of privileges, or information disclosure on vulnerable Windows machines.
Even though attackers would require local user access to abuse the patched flaws, they could also exploit them by remotely dropping malicious tools through various other means on computers running an unpatched NVIDIA GPU Display Driver version.
The table below lists the NVIDIA software products affected such as GeForce and Quadra, versions affected, and the updated versions that are included in this security update. You can download the updates from the NVIDIA Driver Downloads page.
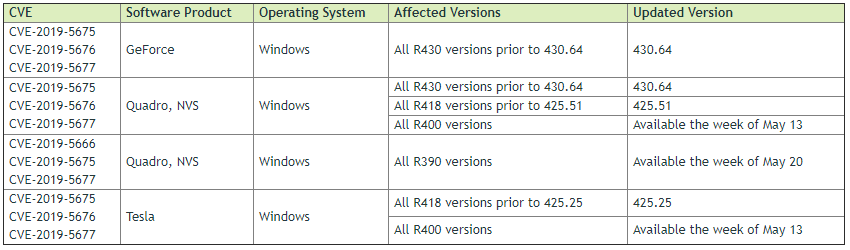
The security issues are tracked as CVE-2019-5675, CVE-2019-5676, and CVE-2019-5677. The risk assessment scores range from 5.6 to 7.7, based on the CVSS V3 standards.
The most severe of the flaws, CVE-2019-5675, could be exploited to launch DoS attacks that could cripple the system, as well as give attackers escalation of privileges and disclose system information.
Discover Affected NVIDIA Drivers in Your Network
If you currently have NVIDIA GPU Display Drivers deployed on your workstations, it’s pretty critical that you update it at the earliest opportunity to ensure that you don’t fall prey to this exploit.
Our custom color-coded vulnerability report can tell you in no time which devices have a vulnerable NVIDIA driver version in place and need to be patched. The report is based on the information that’s currently available. As mentioned in the table above, some patches still have to be issued by NVIDIA.
If you haven’t already, start your free Lansweeper trial and get a report of all affected devices in no time.



