Four MDS attacks have been disclosed today, with Zombieload being considered the most dangerous of them all. Known as Microarchitectural Data Sampling (MDS) attacks, these vulnerabilities allow threat actors to retrieve data that is being processed inside Intel CPUs, even from processes an attacker’s code should not have access. We’ve created a report which lists all Intel CPUs that require Microcode Updates to mitigate these vulnerabilities.
After the discovery of Spectre, Meltdown and Foreshadow vulnerabilities earlier last year, a team of security researchers from multiple universities and security firms have discovered different but more dangerous speculative execution side-channel vulnerabilities in Intel CPUs.
Zombieload is exploited by taking advantage of the speculative execution process, which is an optimization technique that Intel added to its CPUs to improve data processing speeds and performance.
Get a Report of all Affected CPUs in Your Network
Discover Which Intel Processors Need Microcode Updates
Start Your Free TrialAccording to Intel’s security advisory, four MDS attacks have been disclosed:
- CVE-2018-12126 – Microarchitectural Store Buffer Data Sampling (MSBDS) – Codenamed ‘Fallout’
- CVE-2018-12130 – Microarchitectural Fill Buffer Data Sampling (MFBDS) – Codenamed ‘Zombieload’ or ‘RIDL’
- CVE-2018-12127 – Microarchitectural Load Port Data Sampling (MLPDS)
- CVE-2018-11091 – Microarchitectural Data Sampling Uncacheable Memory (MDSUM)
Intel worked with various OS and software vendors to coordinate patches at both the hardware and software level. Microsoft has also released Patch Tuesday software updates to help mitigate the MDS vulnerabilities. According to Microsoft’s MDS security advisory, OS updates are available for Windows and Windows Server, but also SQL Server databases.
Both the hardware (Intel CPU Microcode Updates) and software (OS Security Updates) protections must be installed to fully mitigate MDS attacks.
Which Intel Processors Need CPU Microcode Updates?
We’ve created a report which lists all Intel CPUs that require Microcode Updates to mitigate these Microarchitectural Data Sampling vulnerabilities. You can find the status of available microcode here.
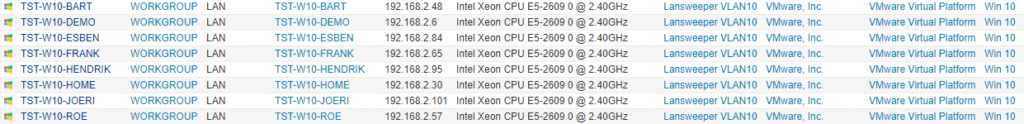
If you haven’t already, start your free trial of Lansweeper to run the Intel Microcode Report.


