
Multiple Vulnerabilities in Firefox Could Allow for Arbitrary Code Execution
Multiple vulnerabilities have been discovered in Mozilla Firefox and Firefox Extended Support Release (ESR), the most severe of which could allow for arbitrary code execution.
Affected Firefox Systems
Mozilla Firefox ESR is a version of the web browser intended to be deployed in large organizations. Successful exploitation of the most severe of these vulnerabilities could allow for arbitrary code execution.
Depending on the privileges associated with the user, an attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. Users whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
One of the critical bugs (CVE-2019-9800) is a memory safety bug that impacts Firefox versions 66 and Firefox ESR 60.6. The Firefox ESR browser is its Extended Support Release version of Firefox, designed for mass deployments.
Firefox 67 Includes Performance Boost & Cryptominer Blocking
The bug fixes coincide with a significant update to the Firefox browser that introduces privacy additions and under-the-hood tweaks to make the browser more competitive with Google Chrome in the speed department. On the privacy front, Mozilla Firefox 67 now blocks crypto mining scripts and a browser’s digital fingerprints.
Get A Report of all Vulnerable Firefox Installations
If you currently have Mozilla Firefox or Firefox EST deployed on your workstations, it’s pretty critical that you update it at the earliest opportunity to ensure that you don’t fall prey to this exploit. Our custom color-coded vulnerability report can tell you in no time which devices have a vulnerable Firefox version in place and need to be patched.
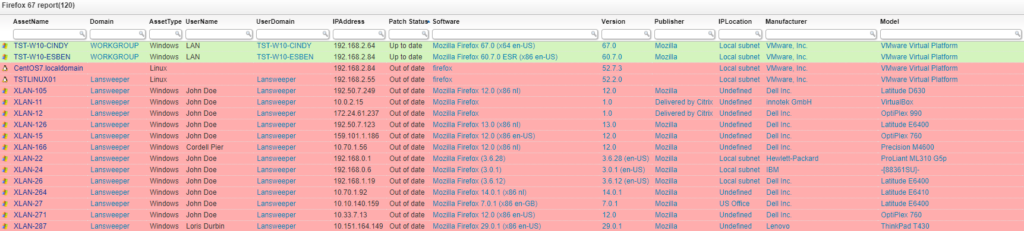
If you haven’t already, start your free Lansweeper trial and get a list of all vulnerable Firefox versions in no time.


