Multiple Vulnerabilities in Google Chrome Could Allow for Arbitrary Code Execution
Google has released Chrome 75 to the Stable desktop channel, with new features and 42 security fixes, with two of them being marked as high severity.
Successful exploitation of the most severe of these vulnerabilities could allow an attacker to execute arbitrary code in the context of the browser, obtain sensitive information, bypass security restrictions and perform unauthorized actions, or cause denial-of-service conditions. The patch for these security vulnerabilities has already been rolled out in a stable Chrome update 75.0.3770.80.
- High – CVE-2019-5828: Use after free in ServiceWorker.
- High – CVE-2019-5829: Use after free in Download Manager.
- Medium – CVE-2019-5830: Incorrectly credentialed requests in CORS.
- Medium – CVE-2019-5831: Incorrect map processing in V8.
- Medium – CVE-2019-5832: Incorrect CORS handling in XHR.
- Medium – CVE-2019-5833: Inconsistent security UI placement.
- Medium – CVE-2019-5834: URL spoof in Omnibox on iOS.
- Medium – CVE-2019-5835: Out of bounds read in Swiftshader.
- Medium – CVE-2019-5836: Heap buffer overflow in Angle.
- Medium – CVE-2019-5837: Cross-origin resources size disclosure in Appcache.
- Low – CVE-2019-5838: Overly permissive tab access in Extensions.
- Low – CVE-2019-5839: Incorrect handling of certain code points in Blink.
- Low – CVE-2019-5840: Popup blocker bypass.
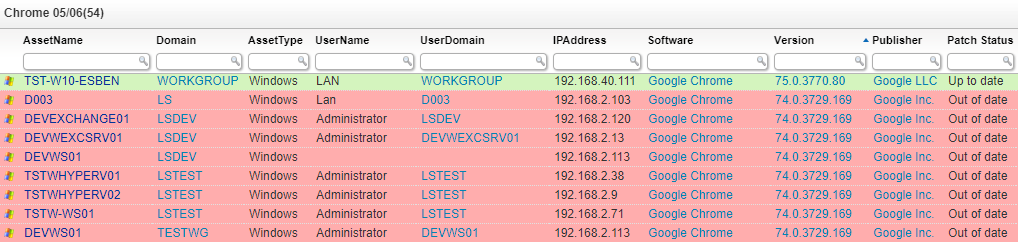
Get A Report of all Outdated Chrome Installations
If you currently have Google Chrome deployed on your workstations, it’s pretty critical that you update it at the earliest opportunity to ensure that you don’t fall prey to these vulnerabilities.
Our custom color-coded report can tell you in no time which devices have a vulnerable Chrome version in place and need to be patched. If you haven’t already, start your free Lansweeper trial and get a list of all vulnerable Chrome versions in no time.
Source: Release Updates from the Chrome Team.