Network scanner: What is it and how do you use it for scanning a network?
The number of technology devices we use in our everyday lives is growing exponentially. Whether we’re at home or at work, we rely on computers and other Internet-connected devices to perform a wide array of tasks. To keep those devices secure and running optimally, it’s important to maintain a detailed inventory of network-connected devices and the software running on them, so that you can roll out updates and patches when necessary, detect and troubleshoot any issues, and ensure the proper security protocols are in place.
But with so many devices on the network, doing this manually is challenging if not impossible. A network scanner automates the process, enabling you to create and maintain a complete network inventory of your network-connected technology assets.
Definition of a network scanner
A network scanner is a software tool or device that is used to identify technology assets connected to a network, such as laptops, servers, routers, printers, mobile devices and more, as well as the services and applications running on those devices. Network scanners can also be used to identify security vulnerabilities and potential threats on a network.
Purpose of using a network scanner
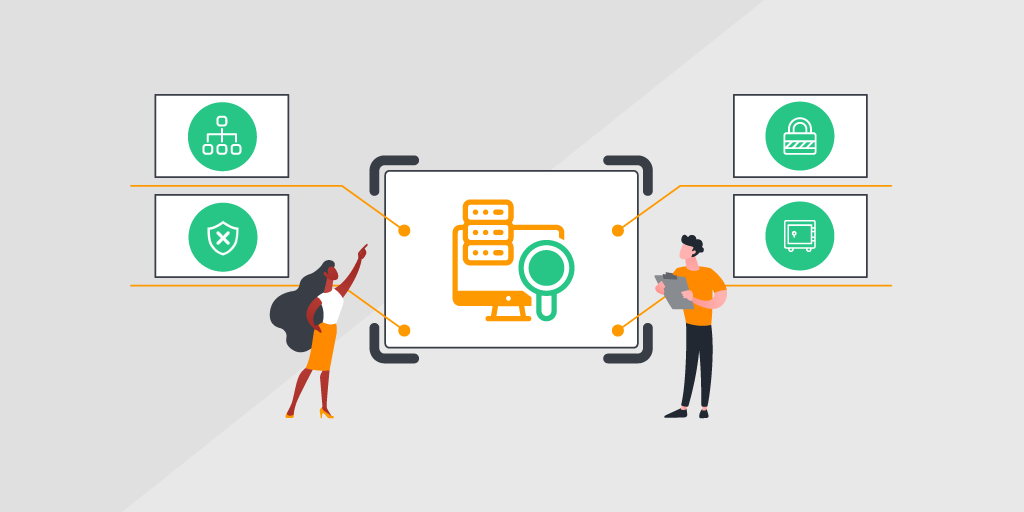
A network scanner is an important tool for network administrators and security professionals and can be used to ensure the security and overall stability of the network infrastructure. Some of the main purposes of a network scanner include:
- Network Mapping: Creating a map of the network topology, which includes all devices and their interconnections. This is useful for identifying the number of devices on the network, their IP addresses and their operating systems.
- Vulnerability Assessment: Identifying vulnerabilities and weaknesses in the network. It can detect open ports, outdated software, misconfigured systems and other security issues that could be exploited by attackers.
- Security Testing: Performing security testing to ensure that the network is properly configured and secured. This includes testing the strength of passwords, network access controls and other security measures.
- Inventory Management: Managing network assets and keep an inventory of all devices and services on the network.

How network scanning works
Before explaining how a network scanner works, it’s important to understand the basics of IP addresses and network protocols
IP addresses are used to identify and route data packets between devices on a network, enabling communication between them. Network protocols, on the other hand, are a set of rules and procedures used by devices on a network to communicate with each other. They define how data is transmitted and received over the network, as well as how devices on the network identify each other and establish connections. Some common network protocols include:
- Transmission Control Protocol/ Internet Protocol (TCP/IP): TCP provides reliable, ordered, and error-checked delivery of data between applications, while IP handles the routing of data packets between devices on the network.
- Hypertext Transfer Protocol (HTTP): HTTP defines how web browsers and web servers communicate with each other to exchange data.
- File Transfer Protocol (FTP): FTP is used for transferring files over the network. It defines how files are transferred, including how they are authenticated and how the data is checked for errors.
- Domain Name System (DNS): DNS translates domain names into IP addresses.
Typically, a network scanner sends packets of data to a range of IP addresses or specific ports on a network, then analyzes the responses it receives. (An IP address is a unique identifier assigned to each device on a network that uses the Internet Protocol for communication.) After it analyzes the responses, the network scanner generates a report of the devices, services and vulnerabilities found on the network, which can be used by system administrators to improve network performance and security.
Scanning Methods: Agent-based versus Agentless
Agentless scanning is a method of network scanning that doesn’t require any software or agent to be installed on the target device. Instead, the scanner sends packets to the devices, then analyzes the response. This method is commonly used for scanning servers, network devices and other infrastructure components.
Agent-based scanning, by contrast, requires a software agent to be installed on the target device before scanning can take place. The agent is responsible for collecting data about the device and its vulnerabilities, then sending that data back to the scanner for analysis. This method is commonly used for scanning workstations, laptops and other endpoint devices.
Both agentless and agent-based scanning have advantages and disadvantages:
- Agentless scanning is easier to implement and manage, because it doesn’t require any software to be installed on the target device. However, agentless scanning does require credentials with sufficient permissions to perform data collection tasks.
- Agent-based scanning can be more complex to implement and manage, as it requires software to be installed on each device. And while it’s less prone to configuration errors, the downside is you have to ensure the software is always up to date.

Techniques used in network scanning
There are various techniques used in network scanning:
- Ping Sweep: Sending a series of ICMP echo requests to a range of IP addresses, to determine which hosts are active and reachable on the network.
- Port Scanning: Sending requests to a range of TCP or UDP ports on a target system to determine which ports are open and what services are running on them. This technique is useful for identifying potential attack vectors and vulnerable services.
- Operating System (OS) Fingerprinting: Analyzing the network traffic to identify the operating system of a target system. This information can be used to identify potential vulnerabilities specific to that OS.
- Banner Grabbing: Sending requests to a target system to retrieve information about the service running on a particular port. This technique can reveal information about the version of the service running and any known vulnerabilities associated with that version.
- Network Mapping: Creating a map of the network topology, including all devices and their interconnections, which can be used to identify potential attack vectors and network misconfigurations.
- Vulnerability Scanning: Using automated tools to identify potential vulnerabilities and security weaknesses.
The technique used by the network scanner depends on the objectives of the scan and the type of information you’re trying to obtain.
Types of network scanners
Some network scanners are designed to be passive and simply listen to network traffic, while others actively send packets to network devices. Here are a few of the most commonly used types of network scanners:
- Ls, and other network components.

Choosing the right network scanner for your needs
The type of scanner you choose depends on many factors, such as the type of network you’re scanning, the size of your network, and what devices you are needing to scan. For example, if you have a lot of operational technology (OT) on your network, your network scanner must be able to support specialized protocols.
You may also be looking for an easy-to-use solution, depending on the technical skillset of your staff. An intuitive interface can help to uncover network asset data quickly and make it instantly actionable. You may also want to find a network scanning tool that provides detailed reporting and insights about vulnerabilities and threats. If cost is a factor, a cloud-based solution may be a preferable option.
Benefits of using a network scanner
As you can imagine, there are numerous benefits to using a network scanner:
- Early detection of network problems: First and foremost, a network scanner can help you proactively identify and fix any vulnerabilities that could potentially open the door to malware or other cyber attacks. A scanner will report back to you what devices and assets are in need of an update or patch, so you can take action to close any gaps in security before an attack occurs. By identifying vulnerabilities and security threats early, a network scanner can help you avoid costly data breaches and downtime that can result from a security incident or outdated equipment or software.
- Better network visibility and management: Network scanners can detect and often identify devices that may be rogue or idle, or Shadow IT such as unsanctioned software, giving you far greater visibility and control over your network infrastructure. What’s more, they completely automate the process of creating a network inventory, saving a tremendous amount of time and manual effort, while reducing the risk of human error.
- Increased network performance and efficiency: With information about your network and infrastructure at your fingertips, you can remediate any issues quickly to maximize the performance and efficiency of your network and infrastructure. Compliance with industry and regulatory standards becomes easy, since you have all the information you need to ensure that the proper policies and protocols are consistently enforced.
Network scanning made simple
Visibility and insights into your network infrastructure has become a must-have capability for enterprise IT organizations as the size and diversity of corporate networks continue to expand. As a result, a network scanner has become an essential tool for network administrators as they strive to optimize the network’s overall health and security, to ensure smooth and secure business operations.
But choosing one that best meets the needs of your business is critical. Lansweeper combines active and passive scanning features and agent-based and agentless scanning, sling with powerful device recognition capabilities, enabling IT organizations to scan, discover, and recognize all technology assets on the network and centralized asset data in an instant. Scannable assets include Windows, Linux, Mac devices, routers, printers, switches, ports, virtual computers, mobile devices, OT, IoT and cloud assets. Learn more or start a free trial today.