- Lansweeper Community
- Knowledge Center
- Knowledge Base
- Requirements
- Network device scanning requirements
- Subscribe to RSS Feed
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Article History
- Subscribe to RSS Feed
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on
03-03-2015
07:30 PM
- edited on
07-26-2023
05:35 PM
by
sophie
![]()
This page provides information on the requirements needed to scan network devices.
Apart from scanning Linux, Unix, Mac and Windows computers, as well as VMware servers, Lansweeper is also capable of scanning network devices. Some examples of network devices are cameras, firewalls, mail servers, music systems, NAS devices, printers, routers, switches, UPS devices, VOIP phones and web servers.
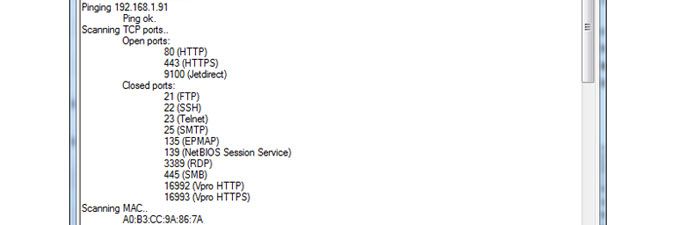
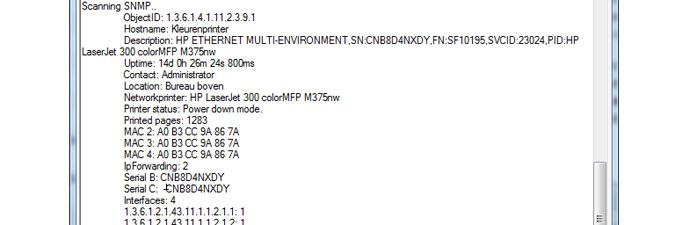
More specifically, Lansweeper can pull data from any device that has one or more of the following protocols enabled: Bonjour, DNS-SD, FTP, HTTP, HTTPS, JetDirect, mDNS, SIP, SMTP, SNMP (SNMPv1, SNMPv2 or SNMPv3), SSDP, SSH, Telnet, UPnP or WMI.
SNMP generally provides Lansweeper with the most detailed device information. Many network devices have SNMP enabled by default and use public and private as their default SNMP community strings (i.e. passwords), public being for read-only access and private for read/write access. A community string with read-only access is sufficient for Lansweeper scanning.
For information on configuring SNMP or another protocol on your device itself, you will need to consult the device documentation, as protocol support and setup differ from device to device. If you are unsure which protocols are enabled on a device, or would like to test your SNMP or SSH credential, run the Devicetester.exe tool on your Lansweeper server. It tests access to the various protocols supported by Lansweeper, and can be found in Program Files (x86)\Lansweeper\Actions\Devicetester.exe.
Don't forget to submit your SNMP or SSH credential in the tester, if relevant. Also make sure to run the tool from the machine hosting the Lansweeper Server service, as this is the only way to simulate exactly which protocols your Lansweeper installation will have access to as well.
New to Lansweeper?
Try Lansweeper For Free
Experience Lansweeper with your own data. Sign up now for a 14-day free trial.
Try NowNew to Lansweeper?
Try Lansweeper For Free
Experience Lansweeper with your own data. Sign up now for a 14-day free trial.
Try Now