- Lansweeper Community
- Knowledge Center
- Knowledge Base
- Installation
- Credential and database security in Lansweeper
- Subscribe to RSS Feed
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Article History
- Subscribe to RSS Feed
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on
12-05-2017
07:30 PM
- edited on
02-16-2024
10:53 AM
by
Nils
![]()
This page explains the security measures built into Lansweeper to protect user data and credentials.
The security and confidentiality of credentials and scanned data are of critical importance in developing the Lansweeper software. Passwords of credentials submitted in Lansweeper are always encrypted prior to being added to your Lansweeper database. The Lansweeper database is also password protected when hosted under Microsoft SQL LocalDB or Microsoft SQL Server. Databases hosted in the deprecated SQL Compact database server can only be accessed locally on the server and don't have a password.
This article highlights some of the measures built into Lansweeper to protect your data and credentials and to eliminate security risks. Topics discussed are:
- Security of submitted scanning and other credentials
- Security of the database and its connection string
- Restrictions on running database scripts
- Security of the web console
- Permissions on installation folders
Security of submitted scanning and other credentials
Certain tasks performed by Lansweeper require you to submit credentials. To remotely scan and deploy on Windows computers for instance, username/password combinations with administrative rights on the computers must be provided. Remote scans of other types of assets also require credentials, with varying degrees of access rights documented in this knowledge base article. Lastly, credentials are also required to access servers used for help desk and alert mailing.
The passwords of submitted credentials are always encrypted prior to being added to your database, the same database that also stores scanned and other data. Once submitted, the passwords are no longer visible in plain text in the web console or database itself. Though the passwords are encrypted, the encryption does need to be reversible, as Lansweeper must eventually pass these credentials to assets and mail servers in order to access them. A key unique to each Lansweeper installation is used to encrypt and decrypt credentials stored in the database. This encryption key is an actual file on the Lansweeper server, making it impossible for anyone to decrypt your credentials unless the Lansweeper server itself is already compromised.
The screenshot below shows the encryption key generated for one specific Lansweeper installation. New Lansweeper installations automatically use a unique key file for credential encryption. Installations that are updated to version 6.0 (or higher) and that only have a single scanning server are also automatically switched to the new method of encryption.
Updated installations that have multiple scanning servers cannot automatically be switched to the new encryption method by the Lansweeper installer. In a multi scanning server setup, the new encryption method can manually be enabled in the Configuration > Server Options menu of the web console.
The encryption key can be found in Program Files (x86)\Lansweeper\Key\Encryption.txt.

Security of the database and its connection string
The Lansweeper software consists of 3 components: database, scanning service and web console. If the database is hosted in the deprecated Microsoft SQL Compact database server, it can only be accessed by processes running locally on the server and has no password. If the database is hosted in SQL LocalDB or SQL Server, it does have a password.
SQL Server databases can also be accessed remotely from other servers in your network, if the necessary firewall and SQL Server configuration is performed and if the correct database password is provided. The database password is automatically randomized under SQL LocalDB and SQL Server to prevent unauthorized access.
You can also specify your own password by following the instructions in this knowledge base article.
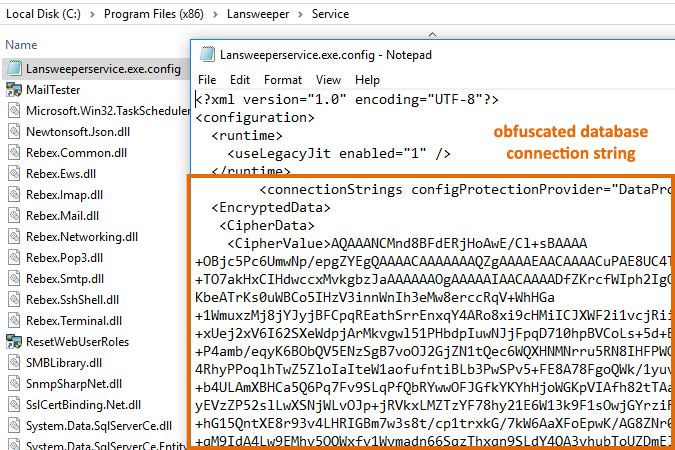
The two configuration files below, found on the scanning server and web server respectively, tell the scanning service and web console which Lansweeper database to access.
Program Files (x86)\Lansweeper\Service\Lansweeperservice.dll.configProgram Files (x86)\Lansweeper\Website\web.configThe database connection strings in these files are obfuscated, making it impossible for someone with access to these files to see where your database is hosted or what its password is.
Connection string modifications must be made using the ConfigEditor tool documented in this knowledge base article.
Restrictions on running database scripts
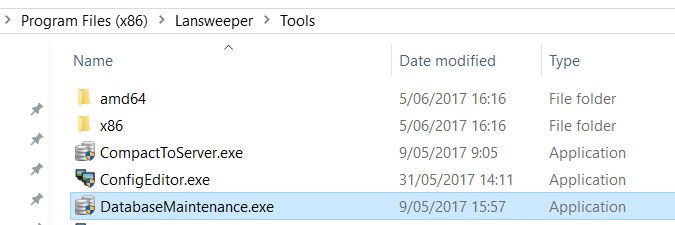
For added security, executing database scripts from the web console has been made impossible. Scripts can now only be run from external tools like the DatabaseMaintenance.exe tool found at Program Files (x86)\Lansweeper\Tools\DatabaseMaintenance.exe on the Lansweeper server.
Tools like SQL Server Management Studio and SQL Compact Toolbox can also be used to run scripts, but connections to SQL LocalDB and SQL Server databases do of course require users to know and submit the database password.
Security of the web console
To ensure that whoever will be managing your Lansweeper installation can access the configuration, the web console is by default accessible to anyone in your network that knows the correct URL. Web console access can easily be restricted to certain users or groups by following the instructions in this knowledge base article.
Restricting access takes just a few minutes and allows you to specify not only who can log in, but also which specific tasks they can perform within the console. Applied web console permissions remain intact after subsequent Lansweeper updates.

The Built-in admin button gives full rights to the console but can be removed. Who can log in with the available login boxes and what they can access can be restricted.
Permissions on installation folders
When you install Lansweeper, most files used by the database, scanning service and web console are copied to Program Files (x86)\Lansweeper on your Lansweeper server. The default permissions on the subfolders located in the Lansweeper installation folder have been made more restrictive where possible, so only necessary users and processes have access.
Was this post helpful? Select Yes or No below!
Did you have a similar issue and a different solution? Or did you not find the information you needed? Create a post in our Community Forum for your fellow IT Heroes!
More questions? Browse our Quick Tech Solutions.
New to Lansweeper?
Try Lansweeper For Free
Experience Lansweeper with your own data. Sign up now for a 14-day free trial.
Try NowNew to Lansweeper?
Try Lansweeper For Free
Experience Lansweeper with your own data. Sign up now for a 14-day free trial.
Try Now
